Why Have Security Questions After Password Authentication?
Jan 20, 2017
Asking security questions after password authentication is not just pointless, it actually makes things less secure.
The practice of using a relatively secure password, combined with a security question to reset it if forgotten is commonplace. The basic idea is that a strong password is easy to forget, so an easy-to-remember answer to a security question provides a convenient way to get around a forgotten password.
It's not very secure. Used as intended security questions undermine the effort involved in using strong passwords. But at least it solves the problem of forgotten passwords.
But lately some sites are asking security questions AFTER password authentication.
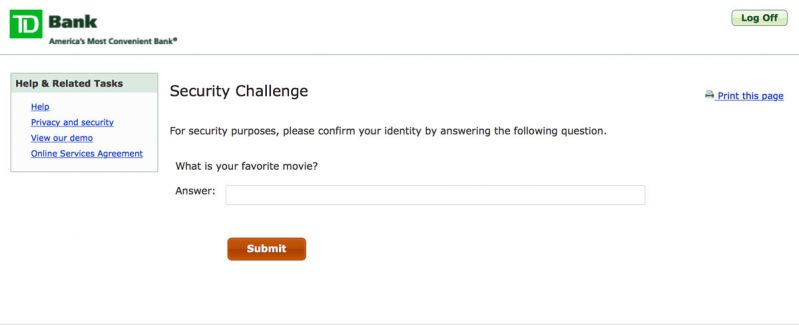
Here is an example. Upon arriving at the website you must first authenticate with a username and password – a relatively secure approach assuming a strong password is in place.

But then, after successfully authenticating with a username and password you have to answer a security question:
This makes no sense. A good password offers some protection, security questions offer almost none. It's like locking your jewels in a shoebox then locking the shoebox in a safe – in the hopes that the shoebox would defeat a burglar that was able to crack the safe...
Passwords
Absent a better approach like two-factor authentication passwords provide a degree of security. The problem is that any security that depends on passwords depends on the strength of the password. Strong passwords offer decent security but are hard to remember, and for most of us will necessitate the use of some kind of password management utility.
Security Questions
Because passwords can be hard to remember security questions (like "what street did you grow up on?") are used as a backup. They aren't as secure as passwords, but they are intended to be easier to remember. The idea is that if you forget your password you can reset it using the security question.
This is clearly not secure – the answers to most security questions could be found by studying someone's Facebook page or through a little social engineering. As a result anyone who is serious about security would use extremely secure answers to these questions – long random strings of characters.
If you were confident in your password manager, and believed that you would always have access to your strong passwords, it was pretty easy. You just answered the question with a long string of random characters and walked away. You wouldn't be able to answer the question (not a problem, because of your password manager you'd never need to) but nobody else could either. It meant nobody (including you) could use the security question to get around the password.
The Problem
The problem is that now, in a completely misguided attempt at improving security, some sites are making you log in first with the (potentially) relatively secure password, and then by answering security questions, which are completely not secure. It's like trying to secure your house by having a heavy-duty deadbolt on the outer door, and a piece of gum to secure the inner door. If you can get by the deadbolt the gum won't slow you down, and if someone has your password the silly security questions aren't going to slow them down. It's inconvenient and a good example of security theater – like somebody said "well, this extra step couldn't hurt so what the hell?".
More Than Just Inconvenient
But it does hurt. It's not just less convenient, its less secure.
The problem is that anyone who was doing it right (using strong passwords and storing them in a password manager) and then answered the meaningless security questions with "burner" answers (that nobody could guess and they could never recall) is now in a bind. Because of this new misguided attempt at security they can now be locked out of accounts because they won't be able to answer security questions.
The (Incredibly Ugly) Solution
The only solution is to revisit any site where you might have used burner answers and replace them with real answers while you still can. If you wait you may go to the site one day, log in with the password, and then be confronted with a security question you can't answer.
The problem of course is that "real" answers to security questions are dangerous, because they make it easy for someone to reset your password and gain access to your account. That means using long random strings of characters (essentially creating additional passwords) and storing them in your password manager – something most password managers were not designed for and do not handle very well.
A much better and more secure alternative already exists, in the form of two-factor authentication, and it's disappointing that it is not more widely used.
Related Content
How To Migrate Google Authenticator To A New iPhone
How To Securely Hide (and Encrypt) Files On Mac OS X
Security Through Obscurity On Mac OS X – Better Solutions
Showing Hidden Files vs Hiding Regular Files in Mac OS X
What Does Incognito/Private Mode Really Mean?
"Your Apple Device has been locked..." Another Scam
Short Guide to (Finding, Sharing, etc.) SSH Keys on Mac OS X
Open Safari Without Opening Windows From The Last Session
Multi-Factor Authentication With Google Authenticator
What is Multi-Factor Authentication?
Category List
Tag List
Technology (1)
Deceptive Order Gathering (10)
Graphic Design (4)
SugarCRM (3)
Flower Buying Tips (23)
Mac OS X (5)
FileMaker (18)
Website Development (17)
Mac OS X Server (11)
Website Cache – Prime & Load (5)
Floral Industry (4)
Litecoin (3)
Bitcoin (3)
Google Authenticator (5)
FloristWare (10)
Online Marketing For Florists (50)
Support Main Street (12)
Industrial Design (2)
Shop Local (12)
Best Practices (32)
Examples of Florist Creativity (6)
Toronto (11)
Pricing (19)
Conventions, Conferences & Trade Shows (4)
Security (33)
Interface Design (7)
Arduino (7)
Concrete5 (1)
SAF (Society of American Florists) (5)
Multi-Factor Authentication (5)
Influence & Persuasion (12)
Floral Management Magazine (14)
Digital Security 2014 (10)
Floral Associations (27)